Increasing cybercrime across the globe has taken a toll on companies and their users. According to the Identity Theft Resource Center (ITRC)’s H1 2022 Data Breach Report, there have been 817 publicly-reported data compromises in the United States this year alone.
While this represents a 4% decrease compared to 2021, the statistics are staggering nonetheless. Ransomware attacks and malware continue to be a main cause of cyber attacks, sounding alarms for everyone to better guard their company data.
To no surprise, tech companies — often conducting the majority of their operations online — haven’t been spared. In 2022, previous data breaches have surfaced that highlight their extent, and real-life impact, on more than 200 million users — along with records of affected data and the damages/expenses involved with recovering information. These incidents underscore the importance of securing IT infrastructure to minimize vulnerabilities and protect critical systems from future attacks.
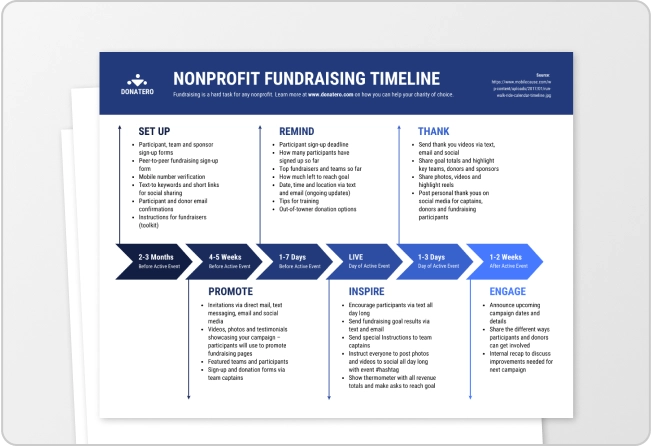
Take a look at this Major Known Data Breaches in Tech 2022 infographic created with our easy-to-edit templates:
Click to jump ahead:
- What is a cybersecurity incident?
- 6 facts you didn’t know about data breaches
- How can I protect my company from a data breach?
What is a cybersecurity incident?
The National Cyber Security Center of U.K. defines a cybersecurity incident — or a cyber attack — as the “breach of a system’s security policy in order to affect its integrity or availability.” Proactively monitoring for these incidents often involves using a data breach scanner to detect unauthorized exposures of system credentials before attackers can exploit them.
There are different types of cyber attacks, and different reasons why an individual or organization would want to break into the security system of another individual, company or organization. Many of these attacks aim to compromise sensitive information, highlighting the importance of securing data in the cloud as a critical component of modern cybersecurity strategies. Let’s review:
Data breaches vs. data leaks
Even though they share similar names, these cyber incidents don’t cover the same risk factors.
A data breach happens when an unauthorized party breaks into a company, individual or organizations system in order to disrupt, steal, control or manipulate private, sensitive or protected information — organizations facing this threat increasingly adopt compliance automation software to streamline audit workflows, track vendor compliance and maintain consistent risk-controls.
In these types of cyber incidents, a company is either forced to pay a ransom, or act involuntarily, so the ransomware releases the hijacked data without revealing it to the public. That’s why it is important to lean on a data privacy framework.
These ransomware attacks entail a major threat to the data security of many businesses. In 2021 alone, 5.9 billion accounts were impacted by data breaches.
Over time, data breaches have become much more frequent, affecting companies of all sizes and industries. So far this year, one of the industries most impacted by sensitive data breaches is the technology industry, underscoring the need for continuous threat exposure management to identify and reduce security risks..
A data leak, on the other hand, happens when sensitive and private information is unknowingly exposed to the public against the victim’s will. This type of cyber incident has historically occurred in many different fields: from leaking pictures of celebrities in new relationships and sharing unreleased album singles, to revealing databases containing projects or even crimes. Because of these data leaks, it is really important to be very careful about your public information. Additionally, in the case of data leaks, you should consider learning how to remove your personal information from the internet.
What’s more, there are other types of cyber attacks that have a purpose not directly linked to the hijacking and exfiltration of data, but instead to the sabotage of a project. These instances slow down or cause an interruption to a website, product or service.
In sum, data breaches have been on the rise for a number of years, with the most impactful cyber attacks happening in the past couple — especially in terms of the cost of damages involved.
6 facts you didn’t know about data breaches
- The damage cost of a data breach in 2022 is approximately $4.35 million.
- The United States is the country most affected by data breaches, encompassing 57% of data breaches and 97% of data records compromised.
- It takes almost six months for a company or a firm to find out about a data breach attack.
- Approximately 68 documents get compromised every second — oh, the Internet, what a beautiful place.
- It takes months for a company to recover from a cyber attack — no, paying a ransom is not the only thing they need to do.
- 6.4 million fake emails are in circulation every day — stop clicking on them, mom.
Now, we don’t want you to be alarmed…but so far in September alone, a dozen cyber attacks have been confirmed. Below, we’ve compiled a timeline of significant Major Data Breaches that have been reported by the media during September of 2022, up to the 20th of this month.
How can I protect my company from a data breach?
We know you don’t have a single new password left in you, but cybersecurity is a never-ending battle. Meaning, if you keep being loyal to that password you created when you were 12… you’ll lose. Adopting enterprise cybersecurity solutions alongside basic security practices can significantly strengthen your defense.
Here are some simple steps you can take to protect your data — for you and your company:
- Instead of using the notes on your phone, invest in a password manager for you and your team — this will allow you to create strong passwords for each important account, and store them all in a safe place.
- Whenever possible, activate 2-Factor authentication to create a second shield of protection for your valuable data. Additionally, implementing a robust Privileged Access Management (PAM) strategy early in your security planning helps in controlling and monitoring the elevated access that is essential to your network’s security.
- Provide your employees with training materials. This process is seamless as there are online platforms like ExamSnap that provide comprehensive training material. This helps them identify suspicious activities or cyber incidents promptly and increases their digital identity security.
- Implement a continuous threat exposure management approach to identify, assess and remediate potential vulnerabilities before they can be exploited. This proactive security posture helps organizations stay ahead of emerging threats rather than simply reacting to breaches after they occur.
- Penetration Testing: Conduct regular penetration testing periodically and after significant changes to your IT infrastructure or applications to ensure ongoing security resilience. This proactive approach helps in fortifying your company’s defenses and reducing the risk of data breaches.
Every day, different job roles enter a more remote and digital environment. Even if you’re not part of a tech company, there’s no doubt defending the information we store on the Internet is extremely important — regardless of company size or sector. Something as simple as installing a Windows VPN can be of great help in defending information.
One simple step is regularly auditing the links your team shares publicly or internally. Using a link checker can help you detect broken or malicious links that could expose your business to phishing attempts or reputational risks — especially when links are embedded in emails, documents, or landing pages.
Data breach statistics reveal 43% of small businesses also fall for cyber attacks that result in the loss of sensitive information, resources and money. Always remember to update your security systems through patch management to protect your company from suffering a data breach.
Also, invest in a privileged access management system to secure your network and enhance visibility while reducing operational complexity.
Additionally, following a cyber essential checklist can provide a structured approach to ensure all critical aspects of cybersecurity are addressed
Alternatively, installing a VPN can also be beneficial as it can help ensure that your network is secure and trackable by hackers or similar cybersecurity threats. You can also install a VPN extenstion as simple way to make a quick VPN connection. For more detailed guidance on protecting your personal data online, consider learning about removing personal data from search sites.
Make your own timeline infographic with Venngage
Found these timeline templates interesting? Have some data you’d like to visualize?
With Venngage’s templates and user-friendly visual editor, you can create your own timeline infographic in under an hour.
To get started, sign up for a free account, pick a template from our library of professionally-designed timelines — including the data breach 2022 infographic featured above — swap in your content and you’re ready to go.




























![Top Known Data Breaches of 2022 [Timeline + Infographic]](https://venngage-wordpress.s3.amazonaws.com/uploads/2022/09/Data_Breach_2022_Blog_Header.png)